This PR fixes `encodeAssertion` to use btoa correctly for SAML assertions that contain non-ASCII. Messages are first manually encoded into UTF-8, and the resulting data is coerced into a JS string that btoa will correctly encode. That intermediary string isn't entirely meaningful -- JS strings are UTF-16, not UTF-8 -- but I think this "hack" of sorts is tolerable given how fleeting its use is. |
||
|---|---|---|
| public | ||
| src | ||
| .env.development.local | ||
| .gitignore | ||
| .nvmrc | ||
| .prettierignore | ||
| .prettierrc.json | ||
| components.json | ||
| LICENSE | ||
| next-env.d.ts | ||
| next.config.js | ||
| package-lock.json | ||
| package.json | ||
| postcss.config.js | ||
| README.md | ||
| screenshot.png | ||
| tailwind.config.js | ||
| tsconfig.json | ||
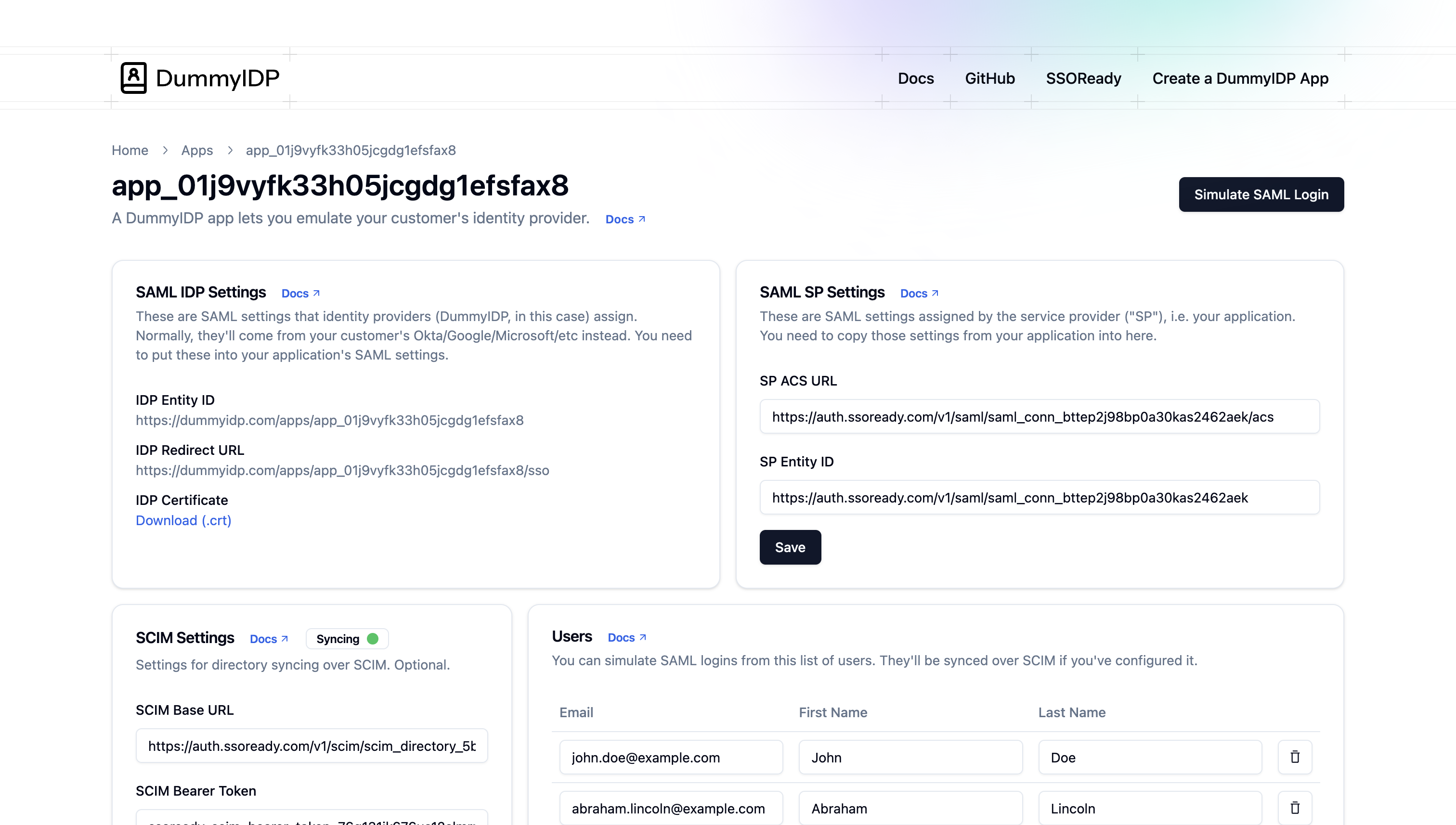
DummyIDP
DummyIDP is a website you can use to test your application's SAML and SCIM support end-to-end. From your application's perspective, it's exactly like the identity provider ("IDP") your customers use, but unlike commercial IDPs there's no "input your email" or "talk to sales" step to use DummyIDP.
DummyIDP implements the "Identity Provider" side of the SAML and SCIM protocols. It is meant for use as a way to test your application's support for the "Service Provider" side of the SAML and SCIM protocols. See "DummyIDP Security Posture" for details.
Local development / self-hosting
DummyIDP is available for free online at https://dummyidp.com. You can also self-host it or hack on it locally.
DummyIDP is a Next.js application. It is deployed in production on Vercel. You can hack on it yourself by running:
npm install
npm run dev